Blog Posts
- Home /
- Blog Posts
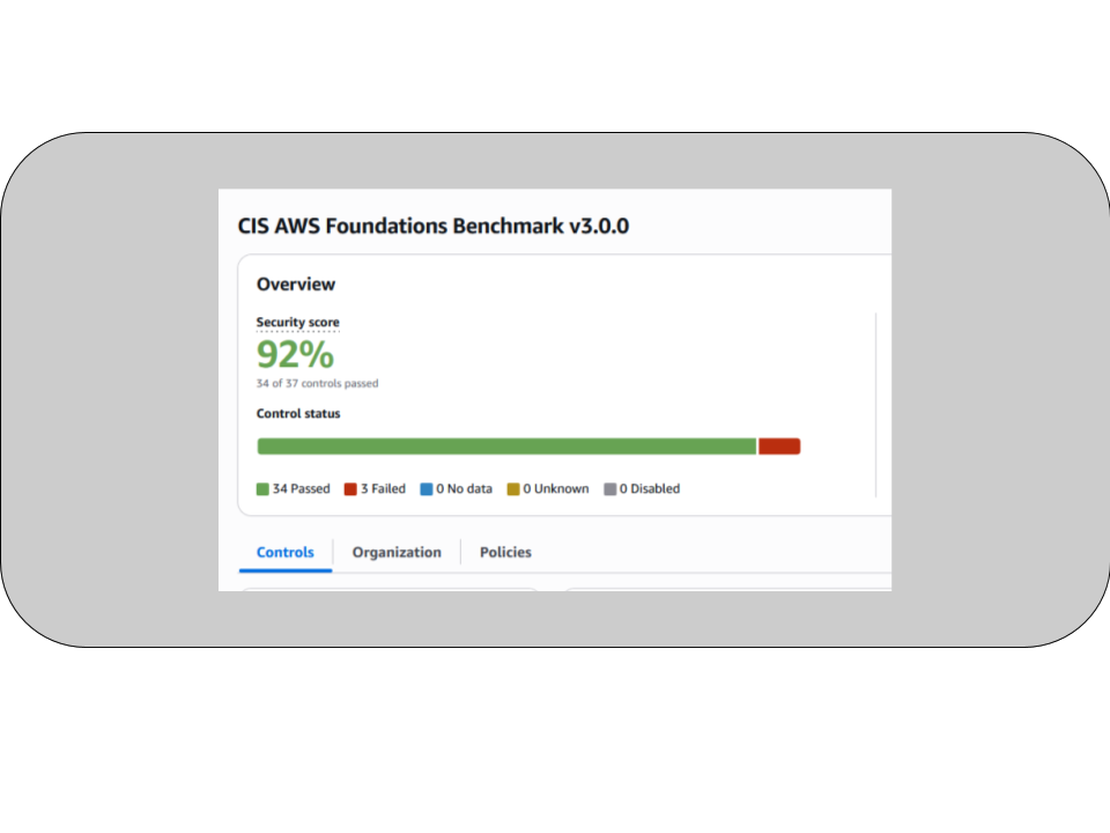
ISO 27001 on AWS: Building Compliance Into the Architecture
The startup I work with builds AI agents for enterprises. I handle the infrastructure. The founders and their engineers build the product.
Read More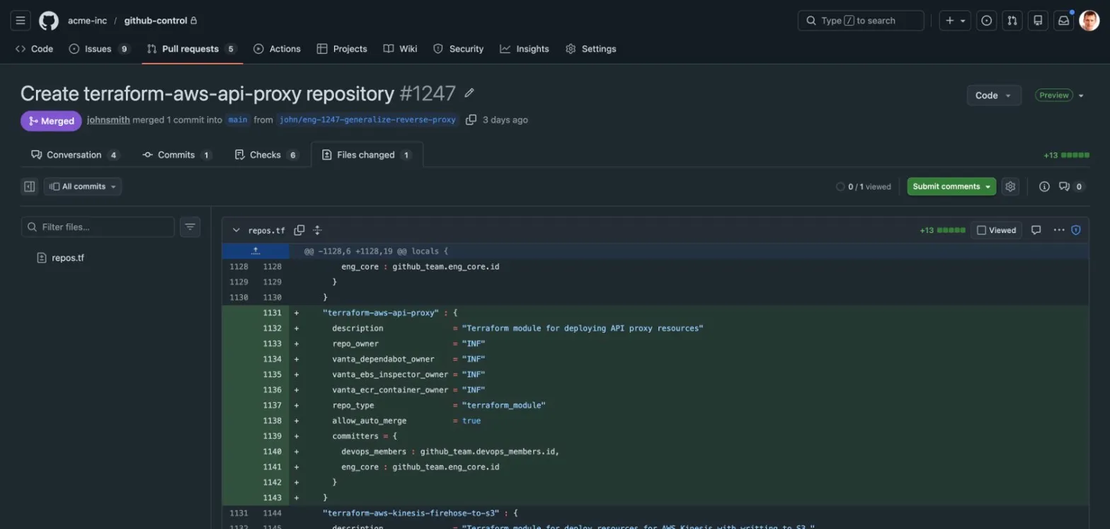
Nobody Wants to Create a New Repo
I run infrastructure for a startup. Over the past two years I’ve built a system that manages the company’s entire GitHub organization — over 100 repositories, their permissions, CI/CD pipelines, AWS environments, and security policies — from a single source of truth.
Read MoreOne Repo to Rule Them All: Managing 100+ GitHub Repos With Terraform
I run infrastructure for a startup. When I joined, the GitHub organization had a handful of repos created by hand through the web UI. Permissions were assigned by clicking buttons. CI/CD was configured manually in each repository. Secrets were copy-pasted.
Read MoreDeploying OpenClaw on AWS Without the Security Disasters
OpenClaw is everywhere right now. 247,000 GitHub stars, an AWS Lightsail blueprint, people running autonomous AI agents from their phones via WhatsApp. It’s legitimately impressive - an open-source agent that can manage your email, execute shell commands, browse the web, and remember context across sessions.
Read MoreDatabase Monitoring Built by DBAs, Not Dashboard Designers
We recently came in as consultants to a startup with PostgreSQL performance problems. They didn’t have a DBA on staff - not unusual for a company their size. They had monitoring: some CloudWatch dashboards, a DataDog subscription. But the data was scattered across tools, and none of it told the complete story.
Read MoreIf It Ain't Stress Tested, It's Broken
On Friday, December 26th, 2025, I released a bugfix for our private PyPI server. The server had been running
for months in a degraded single-instance mode to work around a cache synchronization bug across EFS-backed
containers. With caching enabled, the single instance performed well, but adding more instances would trigger
the bug. The fix removed caching entirely by switching to --backend simple-dir, which meant we could finally
restore high availability.
Stop Paying for Mediocre Code Reviews – Build Exceptional Ones Yourself
If you write or review infrastructure code-Terraform, AWS IaC, CI/CD pipelines, automation scripts - you’ve likely felt the pain points in this story. Maybe you’ve tried commercial AI review tools and found them shallow. Maybe your team struggles with inconsistent reviews. Or maybe you’re scaling quickly and need a way to enforce standards without slowing development down.
Read MoreThree Days, Two Developers: How AI Pair Programming Transformed Good Code into Excellence
Discover how InfraHouse transformed a routine Lambda module into production excellence through disciplined AI collaboration. Same timeline, exponentially better outcome-including ISO 27001 compliance, comprehensive testing, and security patterns discovered after years of experience.
Read MoreFrom Keycloak to Cognito: Building a Self-Hosted Terraform Registry on AWS
A practical engineering story about replacing Keycloak with Cognito to create a self-hosted Terraform registry using Tapir, AWS ECS, and ALB - a simpler, cost-efficient, and fully reproducible setup.
Read MoreVulnerability Management, Part 2: Finding Vulnerabilities in Docker Images
In Part 1
we explored how tools like
OSV-Scanner help you detect
vulnerabilities in application-level dependencies
(think requirements.txt, package-lock.json, etc.).